Security & Compliance
Enterprise-Grade Protection for Sensitive Victim Data
VCPMS SecurityTable of Contents
- Security Overview
- Compliance Framework
- Cloud Security (Microsoft Azure)
- Encryption
- Multi-Factor Authentication (MFA)
- Role-Based Access Control (RBAC)
- Audit Trails
- HIPAA Compliance
- CJIS Compliance
- Business Continuity & Disaster Recovery
- Vulnerability Management
- Secure Software Development Lifecycle
- Privacy Controls
- Confidentiality
- Staff Vetting
- Network Security
- Physical Security
- Work-From-Home Security
- Monitoring & Incident Response
- Why Choose VCPMS Security
1. Security Overview
VCPMS is purpose-built to safeguard the most sensitive categories of personal information in government systems: personally identifiable information (PII), protected health information (PHI), criminal justice records, and financial transaction data. Every architectural decision — from the cloud infrastructure layer to the application code — reflects a security-first design philosophy that places data protection at the core of the platform.
The system employs a multi-layered security approach (defense-in-depth) that spans six critical domains, ensuring that no single point of failure can compromise the confidentiality, integrity, or availability of victim data.
Cloud Infrastructure
Hosted exclusively on Microsoft Azure US data centers with FedRAMP-certified infrastructure, geo-redundant storage, and isolated tenant environments for each state.
Data Encryption
AES-256 encryption at rest with Transparent Data Encryption (TDE), TLS 1.2+ for all data in transit, and Azure Key Vault for centralized key management.
Identity Management
Azure Active Directory integration with mandatory multi-factor authentication, SAML/OAuth federation with state identity providers, and single sign-on (SSO) support.
Network Security
Per-customer firewalls, intrusion detection/prevention systems (IDS/IPS), DDoS protection, VPN-secured administrative access, and public/private subnet segregation.
Audit Controls
Tamper-proof, comprehensive audit logs recording who accessed what data, when, and from where — with full support for compliance reviews and appeals processes.
Regulatory Compliance
Aligned with HIPAA, CJIS Security Policy, FedRAMP, FIPS, NIST 800-53, VOCA/OVC grant requirements, and WCAG 2.1 AA accessibility standards.
2. Compliance Framework
VCPMS operates within a comprehensive regulatory compliance framework that addresses the unique requirements of state victim compensation programs. The platform is designed to meet or exceed the standards mandated by federal and state regulations governing healthcare data, criminal justice information, and government information systems.
| Framework | Status | Scope | Key Requirements Met |
|---|---|---|---|
| HIPAA | Aligned + BAA-capable | Protected Health Information (PHI) | Technical safeguards, access controls, audit controls, integrity controls, transmission security, entity authentication. BAAs executed with state customers; Microsoft Azure BAA covers all Azure services used by VCPMS. |
| CJIS Security Policy | Architected to CJIS controls | Criminal Justice Information (CJI) | Background checks, encryption, access controls, audit logging, media protection, personnel security. Formal third-party attestation in progress. |
| FedRAMP | Azure infrastructure FedRAMP-certified | Cloud infrastructure and services | VCPMS runs on FedRAMP-authorized Microsoft Azure infrastructure. The FedRAMP authorization applies to the Azure platform; VCPMS itself does not hold a separate FedRAMP authorization. |
| FIPS 140-2 | Aligned (via Azure) | Cryptographic modules | Uses FIPS-validated cryptographic modules provided by Azure SQL TDE and Azure Key Vault. |
| SOC 2 Type II | In Progress | Trust services controls | SOC 2 Type II audit is in progress; attestation not yet issued. |
| ISO 27001 | In Progress | Information Security Management | ISMS framework in place, risk assessment methodology, security controls, continuous improvement cycle. |
| NIST 800-53 | Aligned | Security and privacy controls | Access control, awareness/training, audit/accountability, security assessment, system protection. |
| VOCA / OVC | Supported | Grant compliance and reporting | Dedicated VOCA PMT quarterly and VCC annual report generators; performance measures reporting, subgrant monitoring, financial accountability, data integrity. |
| ADA / WCAG 2.1 AA | Built with accessibility in mind | Accessibility | Screen reader compatibility, keyboard navigation, color contrast, alternative text, form labels. Formal WCAG 2.1 AA / Section 508 audit planned. |
HIPAA Compliance
VCPMS handles protected health information including medical bills, treatment plans, counseling records, SANE examination data, and prescription information. All PHI is encrypted both at rest and in transit, access is restricted to authorized personnel on a need-to-know basis, and all access events are logged in tamper-proof audit trails. The platform implements all five categories of HIPAA technical safeguards: access controls, audit controls, integrity controls, transmission security, and entity authentication.
CJIS Security Policy
For states requiring CJIS compliance, VCPMS can be deployed on Azure Government Cloud — a physically isolated cloud environment that meets the most stringent criminal justice data requirements. All ASDCom development team members undergo background checks in accordance with CJIS requirements. Law enforcement reports (police reports, CHP reports, sheriff reports, DOJ records, FBI records, CPS reports) are protected with strict access controls, and all access is logged and auditable.
FedRAMP
VCPMS is hosted on FedRAMP-certified Microsoft Azure infrastructure with continuous monitoring, regular security assessments, and documented incident response procedures. The FedRAMP authorization provides assurance that the underlying cloud infrastructure meets the rigorous security requirements established by the federal government.
NIST 800-53 Security Controls
The platform implements security controls across all 20 NIST 800-53 control families, with particular emphasis on access control (AC), audit and accountability (AU), identification and authentication (IA), system and communications protection (SC), and system and information integrity (SI). Control mappings are documented and available for state security review.
VOCA/OVC Grant Compliance
VCPMS is designed to meet all Victims of Crime Act (VOCA) and Office for Victims of Crime (OVC) grant requirements, including performance measure reporting, subgrant monitoring, financial accountability, and data integrity standards. Built-in reporting templates generate VOCA-compliant reports, reducing the administrative burden on state programs.
ADA/WCAG 2.1 AA Accessibility
All VCPMS portals are designed and tested for WCAG 2.1 Level AA compliance, ensuring that victims, advocates, service providers, and staff with disabilities can fully access and use the system. This includes screen reader compatibility, keyboard-only navigation, sufficient color contrast ratios, alternative text for images, properly labeled form controls, and logical heading hierarchies.
3. Cloud Security (Microsoft Azure)
VCPMS is hosted exclusively on Microsoft Azure, leveraging the industry's most comprehensive set of compliance certifications and enterprise-grade security services. All data is stored and processed within United States data centers only, with no data ever leaving US borders.
Azure Infrastructure
US-Only Data Centers
All VCPMS data resides in Azure data centers located within the continental United States. For CJIS-compliant deployments, Azure Government Cloud provides physically isolated infrastructure meeting the highest government security standards.
Isolated Tenant Environments
Each state customer's data is isolated via a TenantId filter applied automatically to every query by the ABP framework, with independent configuration and encryption keys. Cross-tenant data access is prevented at the application layer. Dedicated per-tenant databases and application servers are available as a deployment option for states whose procurement or security posture requires physical isolation.
Multiple Environments per State
Each customer receives separate environments for production, staging, and testing. Environment configurations are maintained independently, ensuring that development activities never impact production data or availability.
Infrastructure-as-Code (Bicep)
All infrastructure is defined declaratively using Azure Bicep templates, ensuring consistent, repeatable, and auditable deployments. Infrastructure changes go through the same code review and approval process as application code.
Azure Security Services
| Azure Service | Purpose | Security Benefit |
|---|---|---|
| Azure App Services | Application hosting | Built-in DDoS protection, SSL/TLS termination, IP restrictions, managed identity authentication |
| Azure SQL Database | Data storage | Transparent Data Encryption (TDE), geo-replication, advanced threat protection, dynamic data masking, row-level security |
| Azure Key Vault | Secret and key management | FIPS 140-2 Level 2 validated HSMs, access policies, rotation scheduling, audit logging of all key operations |
| Azure Functions | Background processing | Isolated execution, managed identities, VNet integration, consumption-based scaling |
| Azure Monitor / App Insights | Monitoring and telemetry | Real-time alerting, anomaly detection, centralized logging (JSON-structured), Kusto query analytics |
| Azure Active Directory | Identity and access management | MFA, conditional access policies, SAML/OAuth federation, identity protection, privileged identity management |
| Azure API Management | API gateway | Rate limiting, IP filtering, JWT validation, request/response transformation, API key management |
High Availability
VCPMS is architected for high availability with multiple layers of redundancy to ensure uninterrupted service for victim compensation programs.
- Geo-dispersed redundant servers — Application instances run across multiple availability zones within a region, with disaster recovery instances in a geographically separate region
- Load balancing — Azure Load Balancer distributes traffic across healthy instances, automatically routing around failures
- Elastic scaling — Application tiers scale automatically based on demand, handling peak loads (e.g., annual reporting deadlines) without performance degradation
- Auto-scaling rules — CPU, memory, and request-based scaling rules trigger additional capacity within seconds of demand increases
Screenshot: Azure infrastructure architecture diagram showing multi-region deployment with failover — Available upon request
4. Encryption
VCPMS implements comprehensive encryption to protect victim data at every stage of its lifecycle. All encryption mechanisms meet or exceed federal standards (FIPS 140-2), and encryption keys are managed centrally through Azure Key Vault with strict access controls and rotation policies.
Encryption at Rest
| Data Store | Encryption Method | Standard |
|---|---|---|
| Azure SQL Database | Transparent Data Encryption (TDE) | AES-256 |
| Azure Blob Storage (documents) | Azure Storage Service Encryption (SSE) | AES-256 |
| Backups and replicas | Encrypted at source; encryption travels with data | AES-256 |
| Virtual machine disks | BitLocker (Windows) / dm-crypt (Linux) | AES-256 |
| Temporary storage / cache | In-memory only; no persistent cache of PII | N/A |
Encryption in Transit
- TLS 1.2 or higher enforced on all connections — older protocols (TLS 1.0, 1.1, SSL) are explicitly disabled
- HTTPS enforced for all web traffic — HTTP requests are automatically redirected to HTTPS
- SFTP / SSH preferred for file transfer integrations (e.g., payment batch exports, document imports)
- All wireless communications encrypted — WPA3 or WPA2-Enterprise required for any wireless access
- API communications secured with TLS 1.2+ plus API key and JWT token authentication
- Database connections encrypted with TLS between application tier and Azure SQL
Key Management
Azure Key Vault
All encryption keys, certificates, and secrets are stored in FIPS 140-2 Level 2 validated Hardware Security Modules (HSMs) within Azure Key Vault. Access is controlled by Azure AD policies with full audit logging.
6-Month Key Rotation
Encryption keys are rotated on a 6-month schedule (or more frequently if required by policy). Rotation is automated and does not require application downtime or data re-encryption.
Managed Identities
Application services authenticate to Azure resources using managed identities, eliminating the need for credentials in code or configuration files. No passwords or connection strings are stored in application settings.
Secrets Separation
Secrets are strictly separated from application configuration. Environment-specific values are injected at deployment time from Key Vault references, never committed to source control.
Encryption Integrity
- Regular updates — Encryption libraries and TLS configurations are updated promptly when new vulnerabilities are discovered
- Vulnerability scanning — Automated scans verify that only approved cipher suites and protocols are in use
- Documented procedures — Key generation, rotation, revocation, and destruction procedures are formally documented and auditable
- Compliance verification — Encryption configurations are verified against FIPS 140-2 and NIST guidelines during each security assessment
5. Multi-Factor Authentication (MFA)
Multi-factor authentication is configurable per tenant and can be required for all or specific user categories (back-office staff, victims, providers, advocates, law enforcement). When enabled, MFA is enforced at every login.
Authentication Methods
| Method | Shipped / Optional | Description |
|---|---|---|
| TOTP Authenticator Apps | Shipped | Time-based one-time passwords via Microsoft Authenticator, Google Authenticator, or any RFC 6238-compatible app. QR-code enrolment at first login. |
| QR-Code Login | Shipped | SignalR-backed passwordless login (QrLoginHub) — a desktop session displays a QR code that a pre-paired mobile app scans to authenticate. |
| Security Questions | Optional | Challenge / response available as an account-recovery fallback. |
| Azure AD Conditional Access | Deployment option | When the tenant integrates VCPMS with Azure AD, biometrics (Windows Hello, Touch ID, FIDO2), device-compliance checks, and location-based restrictions can be enforced at the IdP. These controls are provided by Azure AD, not by the VCPMS application itself. |
Identity Federation
- JWT Bearer + OpenIddict — Built-in authentication pipeline. Local accounts are the default; OpenIddict-based OAuth 2.0 / OIDC federation is available for integration with state identity providers.
- SAML / OAuth Federation — Integration-ready for state identity providers (e.g., Okta, Azure AD, ADFS, PingFederate). Named integrations require tenant-specific configuration and are not activated by default.
- SSO Token Acceptance — Once authenticated through a federated identity provider, users receive a signed SSO token valid for the configured session duration.
Session and Token Controls
- Maximum token validity: 24 hours — tokens expire and require re-authentication
- Idle session timeout: Configurable per tenant (typically 15-30 minutes of inactivity)
- Concurrent session limits: Administrators can restrict users to a single active session
- Session termination: Administrators can force-terminate any user session immediately
Password Policy
| Policy | Requirement |
|---|---|
| Minimum length | 12 characters |
| Complexity | Must include uppercase, lowercase, numbers, and special characters |
| Rotation | 90-day mandatory password change |
| Reuse prevention | Last 4-5 passwords cannot be reused |
| Storage | Passwords are salted and hashed (bcrypt/PBKDF2) — never stored in plaintext |
| Breach detection | Passwords checked against known breach databases (Azure AD Password Protection) |
Login Protection
Progressive Delays
After failed login attempts, progressive delays are applied to prevent brute-force attacks. Delay intervals increase exponentially with each consecutive failure.
reCAPTCHA
Google reCAPTCHA is presented after multiple failed attempts to distinguish automated attacks from legitimate user errors.
Account Lockout
Accounts are temporarily locked after a configurable number of failed attempts (default: 5). Lockout duration is configurable per tenant policy.
IP Filtering & Input Validation
Suspicious IP addresses can be blocked. All login form inputs are validated and sanitized to prevent injection attacks through authentication endpoints.
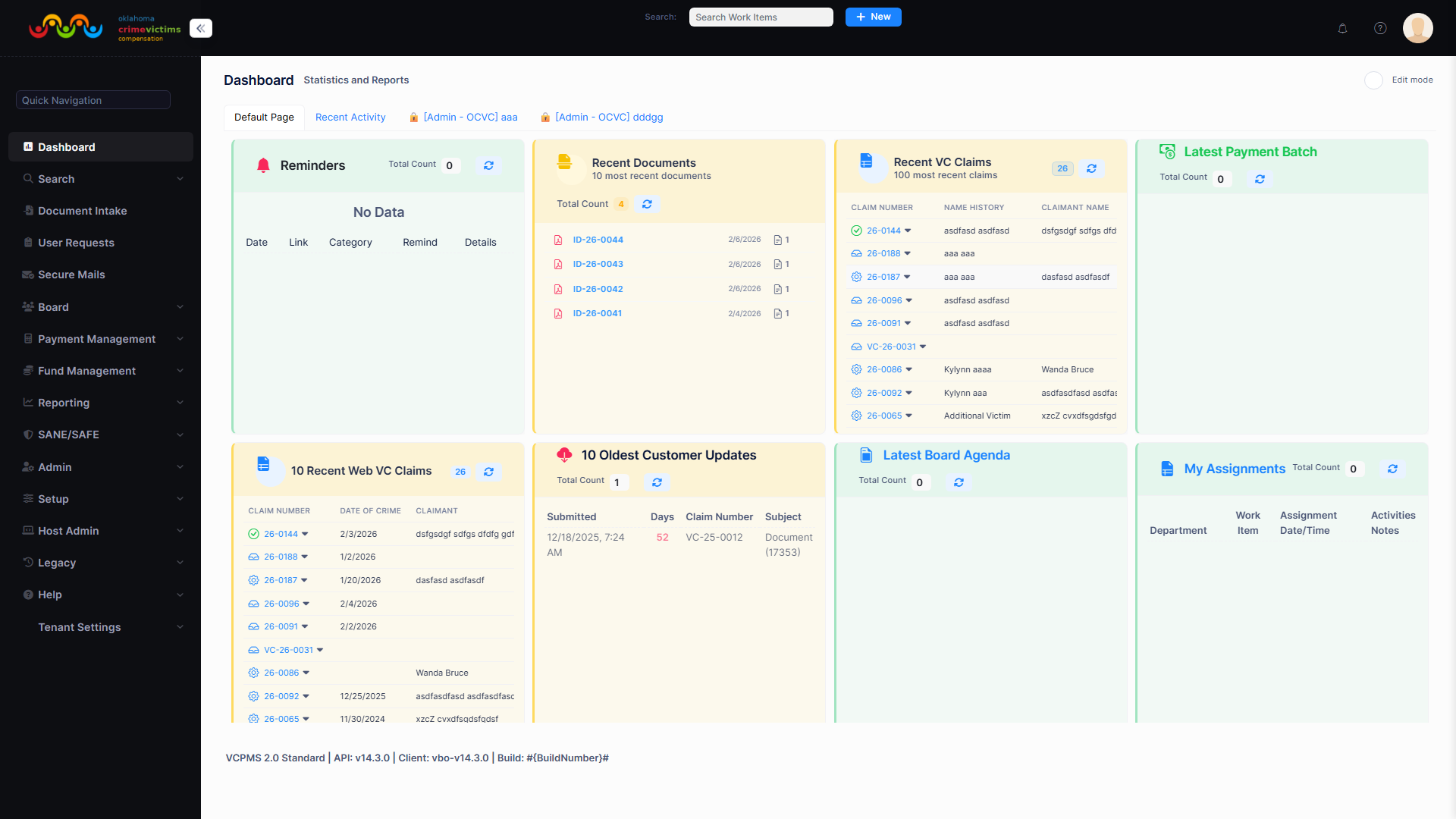
Tenant security settings including MFA enforcement, password policies, and session timeout configuration
6. Role-Based Access Control (RBAC)
VCPMS implements a comprehensive, four-level permission architecture that controls access at every layer of the application — from which pages a user can see, down to which fields are visible and which documents can be accessed. This granular approach ensures that every user sees only the information required for their specific role and responsibilities.
4-Level Permission Architecture
| Level | Scope | Description | Example |
|---|---|---|---|
| System Level | Platform-wide | Controls access to major application modules and system administration functions | Access to Claims module, Payment module, Admin console |
| Page Level | Individual screens | Determines which pages within a module a user can view or interact with | View Claims List, Access Payment Batch screen, Open Reports |
| Field Level | Individual data fields | Controls visibility and editability of specific fields on each page | View SSN (masked), Edit payment amount, Hide victim address |
| Document Level | Individual documents | Governs access to uploaded and generated documents based on type and classification | View police reports (LEA only), Download medical records (authorized staff only) |
5 Permission Types
Each permission type can be independently assigned at every level, creating fine-grained control. For example, a user may have View and Search permissions on claims but no Add, Update, or Delete permissions — creating an effective read-only auditor role.
Data Masking
Sensitive data is automatically masked based on user permissions and context to prevent unauthorized exposure of PII.
- Social Security Numbers (SSN) — Displayed as
***-**-1234(last 4 digits only) to all users except those with explicit SSN access permissions - Victim Date of Birth — Hidden or masked on screens and reports for users without demographic access
- Protected Notes — Confidential case notes visible only to designated staff roles
- PII on Screens and Reports — Dynamic masking applied based on the user's role, the data classification, and the context (screen display vs. printed report)
- Anonymous Identifiers — External-facing portals use anonymous case numbers rather than victim names or personal identifiers
Multi-Tenant Data Isolation
- Tenant isolation on all entities — Every database record includes a mandatory
TenantIdfield, and the ABP framework automatically filters all queries to prevent cross-tenant data access - Jurisdiction scoping — Users can only access data within their assigned organizational unit and jurisdiction
- External user restrictions — Victims, service providers, advocates, and law enforcement officers can only see their own cases, claims, and submissions
User Categories
| Category | Portal | Typical Roles | Data Access Scope |
|---|---|---|---|
| VboUser | VCPOffice | Claims Analysts, Supervisors, Program Managers, Financial Officers | All claims and data within their organizational unit and assigned work queues |
| VcaUser | VCPOnline | Victims, Claimants, Applicants | Only their own claims, applications, and communications |
| SpaUser | VCPProvider | Service Provider Staff, Billing Coordinators | Only claims and payments associated with their service provider organization |
| AdvUser | VCPAdvocate | Victim Advocates, Case Managers | Only clients they are authorized to represent, with victim consent |
| LeaUser | VCPAgency | Law Enforcement Officers, Agency Liaisons | Only cases linked to their agency's reports, with no access to financial data |
| Board Members | VCPOffice (limited) | Board of Control Members, Hearing Officers | De-identified case summaries for board hearings and appeals decisions |
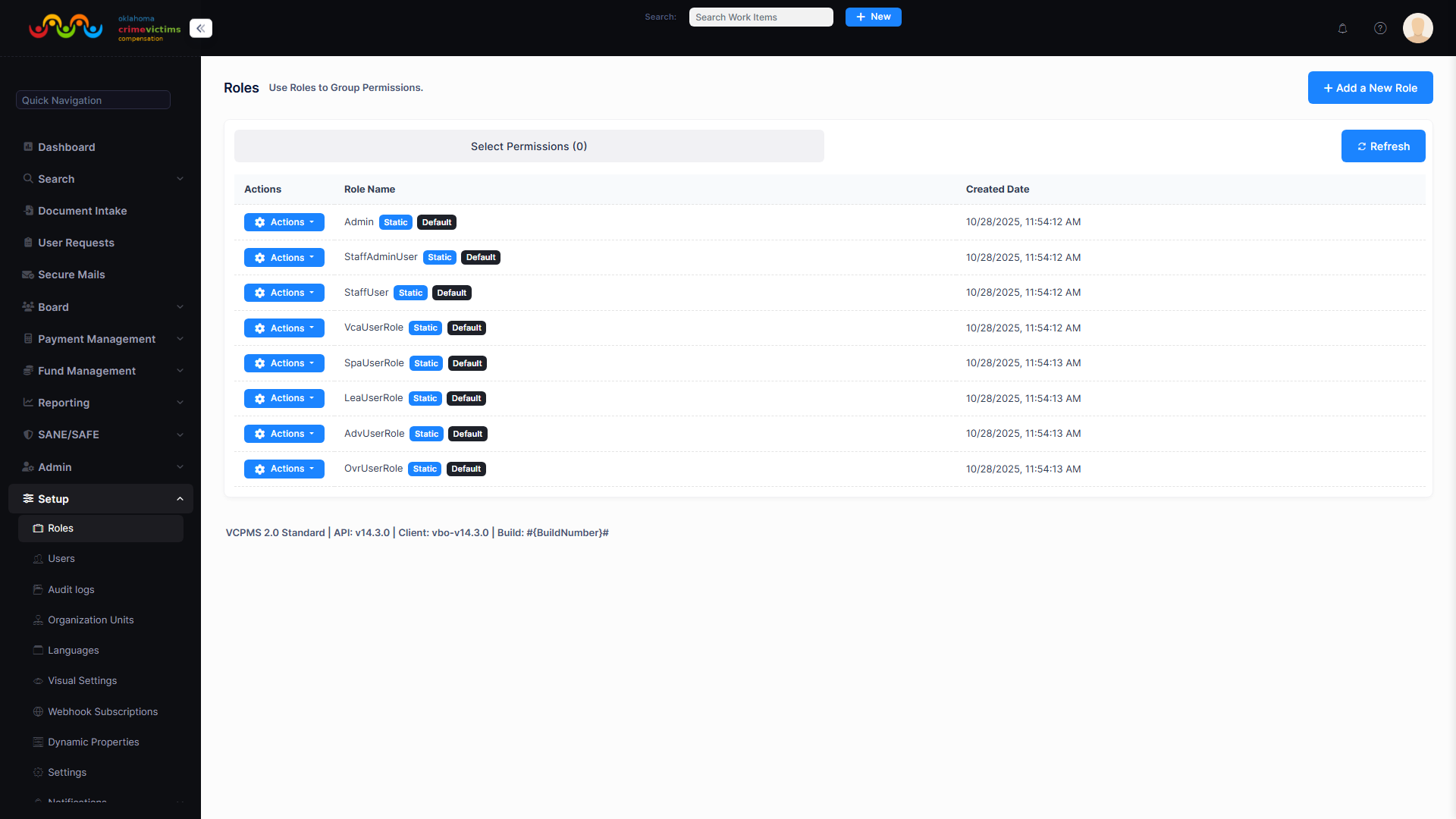
Role Management interface with permission assignment across system, page, field, and document levels
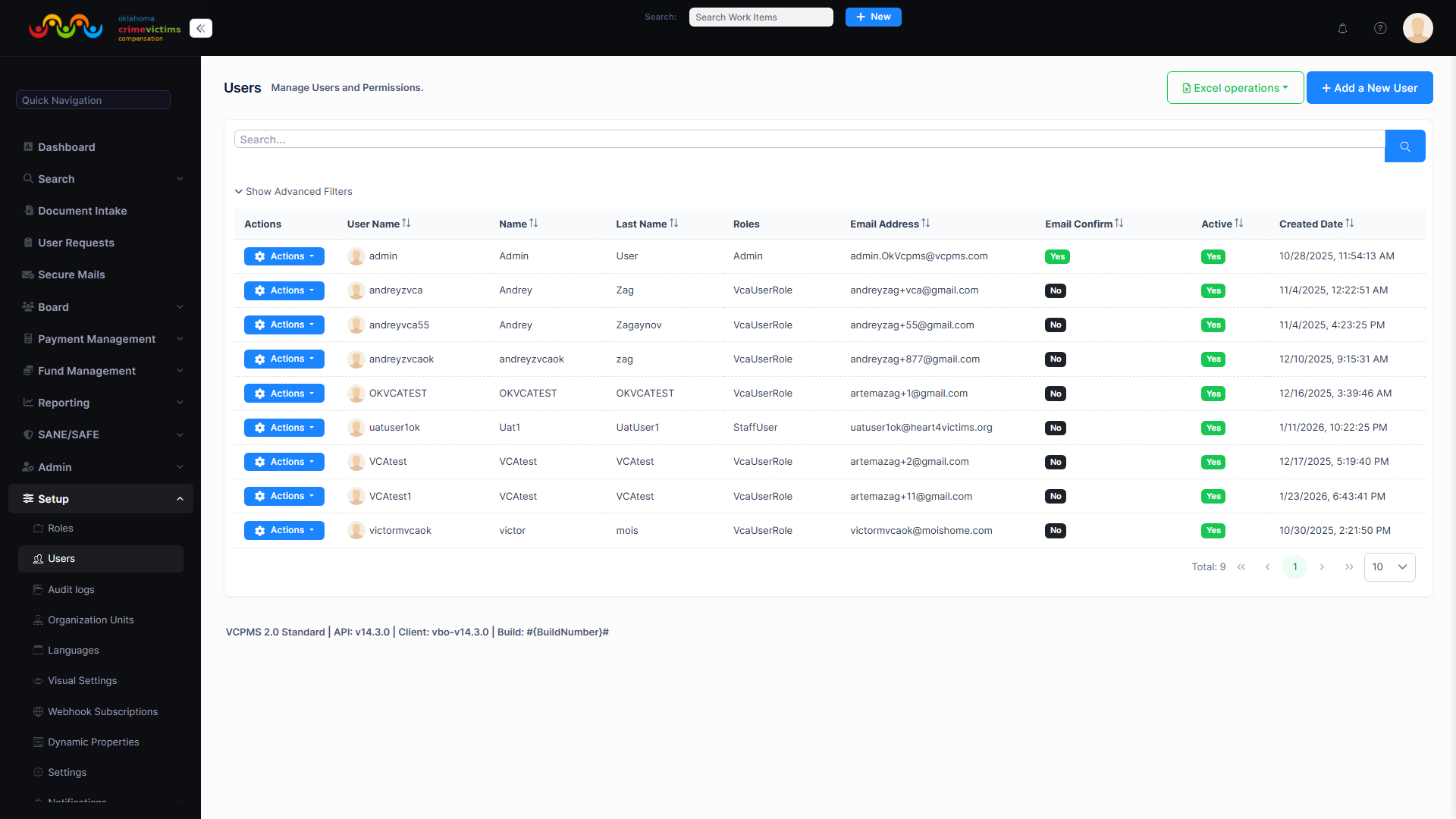
User Management interface showing user accounts with assigned roles and permission levels
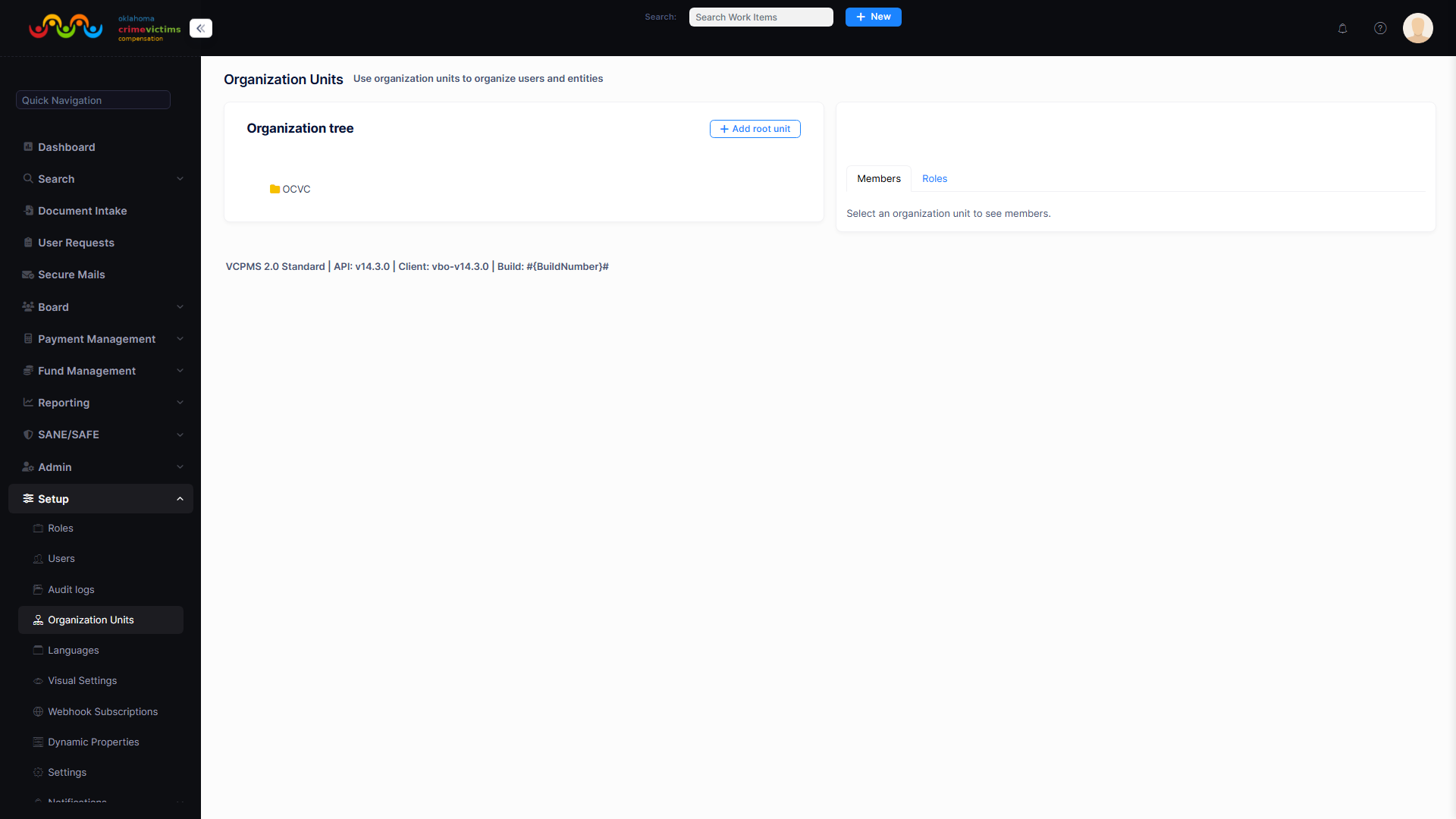
Organization Units hierarchy for jurisdiction-based access scoping and data isolation
7. Audit Trails
VCPMS maintains comprehensive, tamper-proof, read-only audit trails that record every significant action performed within the system. Audit records capture who performed an action, what was changed, when the change occurred, and where the request originated (IP address, client type, session identifier). These trails are essential for compliance reviews, appeals processes, fraud investigation, and unauthorized access detection.
Audited Events
| Category | Events Tracked | Data Captured |
|---|---|---|
| Authentication | Login attempts (success/failure), logout, MFA challenges, password changes, account lockouts | User ID, IP address, timestamp, device fingerprint, result |
| Data Access | Record views, searches, exports, report generation, document downloads | User ID, entity type, record ID, fields accessed, timestamp |
| Claim Decisions | Approvals, denials, withdrawals, state changes, assignment transfers | User ID, claim ID, previous state, new state, reason, timestamp |
| Financial Actions | Payment approvals, batch processing, fund transfers, amount changes | User ID, payment ID, amount, source fund, payee, approval chain |
| Document Actions | Uploads, downloads, deletions, classifications, merges, splits, archives | User ID, document ID, action type, file metadata, timestamp |
| User Management | Account creation, deactivation, role changes, permission modifications | Admin user ID, target user ID, changes made, effective date |
| Permission Changes | Role assignment, permission grants/revocations, organizational unit changes | Admin user ID, target role/user, permissions modified, before/after state |
| Configuration Changes | Workflow config changes, system settings, notification rules, report definitions | Admin user ID, config area, previous value, new value, timestamp |
| Fund Changes | Source fund creation, balance adjustments, fund allocations, depletion alerts | User ID, fund ID, previous balance, new balance, reason |
| Batch Operations | Payment batch creation, approval, processing, export to state financial systems | User ID, batch ID, item count, total amount, processing status |
| Electronic Signatures | Application signatures, consent forms, appeal acknowledgments | Signer identity, document signed, signature timestamp, IP address |
Audit Trail Characteristics
- Tamper-evident — Audit records (
DomainEntityActivity,TriggerActionLog) are treated as write-once, append-only by the application. No application user or administrator can modify or delete audit entries through any application interface. - Read-only at application layer — Audit data is accessible for review and export. Database-level immutability relies on Azure SQL role separation and access controls; SQL Server Ledger tables can be enabled at the deployment level for cryptographic immutability where required.
- Timestamped — All entries use UTC timestamps synchronized via Azure time services for accuracy across time zones
- Linked to identity — Every audit entry is tied to an authenticated user identity, including federated identities from state IdPs
- Retained per policy — Audit retention periods are configurable per tenant to meet state-specific regulatory requirements (typically 7+ years)
Audit Reporting
- Compliance reviews — Generate audit reports for scheduled compliance audits, covering any date range, user, entity type, or action category
- Appeals support — Complete audit trails for individual claims provide the evidentiary basis for appeals and hearings
- Unauthorized access tracking — Automated alerts for unusual access patterns (e.g., accessing records outside assigned caseload, after-hours access, bulk data exports)
- Jurisdiction-specific trails — Audit data is scoped to each tenant, ensuring state-specific audit requirements are met without exposing data from other jurisdictions
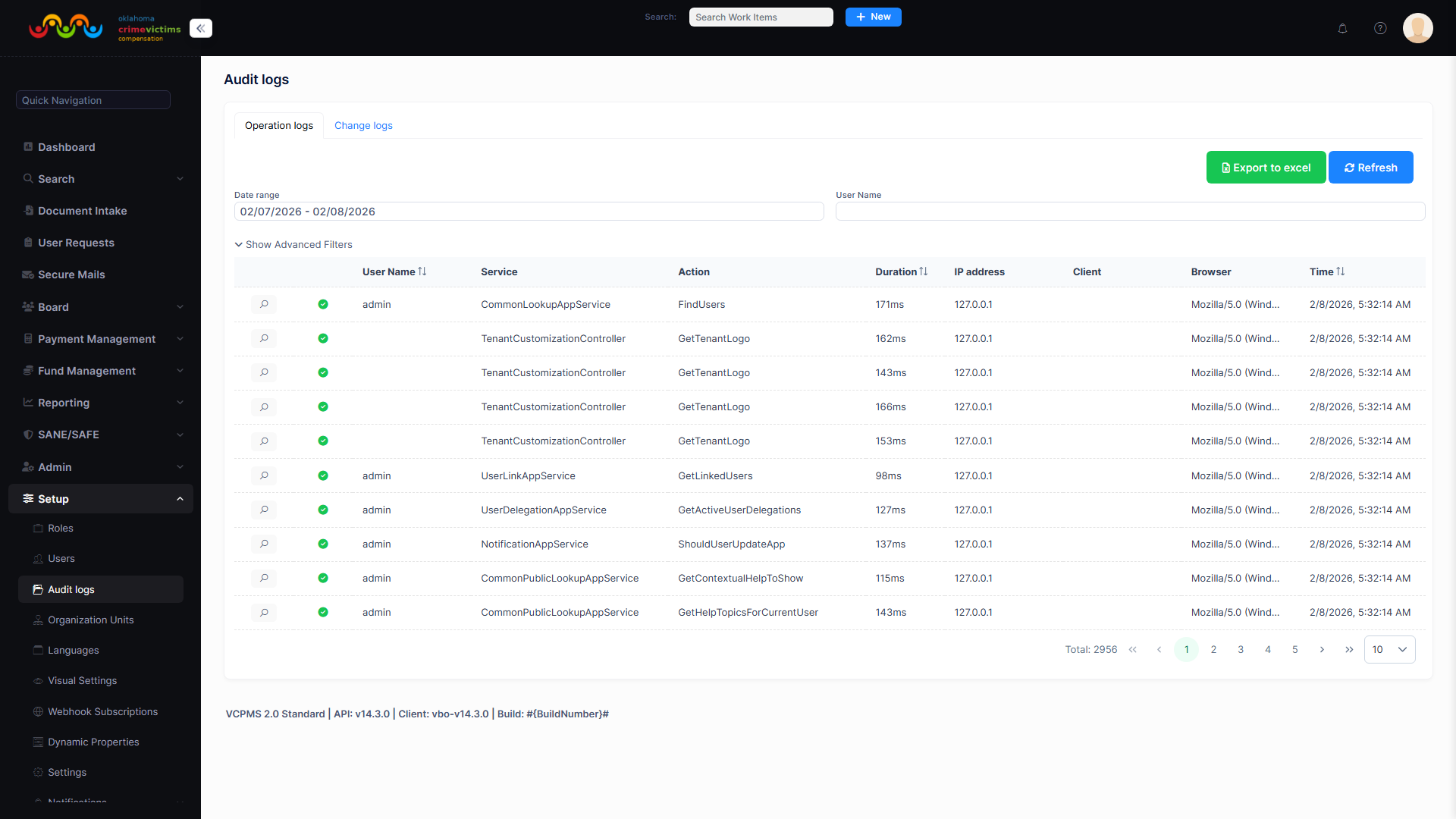
Audit Log viewer with detailed event history, filterable by date range, user, action type, and entity
8. HIPAA Compliance
Victim compensation programs routinely process protected health information (PHI) including medical bills, treatment plans, counseling records, Sexual Assault Nurse Examiner (SANE) examination data, and prescription information. VCPMS implements the full suite of HIPAA technical safeguards to ensure this data is handled in strict compliance with federal health information privacy law.
Health Information Protected by VCPMS
| PHI Category | Examples | Protection Measures |
|---|---|---|
| Medical Bills | Hospital invoices, emergency room charges, surgical bills, ambulance transport | Encrypted storage, role-based access, masked on non-financial screens |
| Treatment Plans | Mental health treatment plans, physical therapy schedules, rehabilitation programs | Restricted to authorized claims analysts and medical review staff |
| Counseling Records | Therapist notes, session summaries, psychological assessments | Enhanced access controls, separate permission category, audited access |
| SANE Data | Sexual assault examination reports, forensic evidence documentation | Highest sensitivity classification, restricted distribution, encrypted at all layers |
| Prescriptions | Medication records, pharmacy bills, drug formulary information | Encrypted storage, access limited to financial processing staff |
HIPAA Technical Safeguards
Access Controls
Unique user identification, emergency access procedures, automatic logoff, and encryption/decryption mechanisms ensure that only authorized individuals access PHI in any format.
Audit Controls
Hardware, software, and procedural mechanisms record and examine activity in systems that contain or use PHI, providing complete access histories for any protected record.
Integrity Controls
Policies and procedures protect PHI from improper alteration or destruction. Database integrity checks, checksums, and version tracking ensure data has not been tampered with.
Transmission Security
All PHI transmitted over electronic networks is encrypted with TLS 1.2+. Integrity controls verify that PHI has not been modified during transmission.
Entity Authentication
Procedures verify that any person or entity seeking access to PHI is who they claim to be, through multi-factor authentication and identity federation.
9. CJIS Compliance
Many victim compensation claims involve criminal justice information (CJI) including police reports, arrest records, court documents, and law enforcement investigation details. VCPMS aligns with the FBI Criminal Justice Information Services (CJIS) Security Policy to ensure this data is handled with the strictest protections required by federal and state law enforcement agencies.
CJIS Security Policy Alignment
| CJIS Policy Area | VCPMS Implementation |
|---|---|
| Information Exchange | All CJI exchanged between law enforcement portals and VCPMS is encrypted with FIPS-compliant algorithms over TLS 1.2+ connections |
| Security Awareness Training | All ASDCom personnel with access to CJI-containing systems complete annual CJIS security awareness training |
| Incident Response | Documented incident response plan specific to CJI breaches, with notification procedures aligned to CJIS requirements |
| Auditing and Accountability | All access to CJI is logged with user identity, timestamp, action, and result; logs are retained per CJIS retention requirements |
| Access Control | CJI access limited to background-checked personnel with specific role assignments; least-privilege principle enforced |
| Identification and Authentication | Advanced authentication (MFA) required for all CJI access; unique user identification; session management controls |
| Configuration Management | All CJI-related system configurations documented, change-controlled, and audited; baseline configurations maintained |
| Media Protection | CJI on removable media is encrypted; media sanitization procedures follow NIST SP 800-88 guidelines |
| Physical Protection | Azure data centers meet CJIS physical security requirements; Azure Government Cloud available for enhanced isolation |
| Personnel Security | Background screening for all ASDCom personnel; state-level fingerprint-based background checks for CJIS access |
Law Enforcement Records Protection
VCPMS protects the following categories of law enforcement reports and criminal justice data with CJIS-compliant controls:
- Police reports — Municipal and county law enforcement incident reports
- CHP reports — California Highway Patrol accident and incident reports
- Sheriff reports — County sheriff department investigation reports
- DOJ records — Department of Justice criminal history and case records
- FBI records — Federal Bureau of Investigation case information
- CPS reports — Child Protective Services investigation reports
Background Checks on Development Team
All ASDCom development team members undergo comprehensive background checks including criminal record searches, employment verification, and reference checks. Personnel with access to systems containing CJI undergo additional state-level fingerprint-based background checks in accordance with CJIS policy requirements. Background check results are maintained in confidential personnel files and reviewed annually.
10. Business Continuity & Disaster Recovery
VCPMS is engineered for maximum resilience with comprehensive business continuity and disaster recovery (BC/DR) capabilities. The platform is designed to maintain operations even during significant infrastructure failures, with automated failover mechanisms that minimize or eliminate service interruptions for victim compensation programs.
Backup Strategy
| Backup Type | Frequency | Retention | Details |
|---|---|---|---|
| Full Database Backup | Daily (automated) | 30 days | Complete snapshot of all databases including schema, data, and indexes |
| Incremental Backup | Hourly (automated) | 7 days | Captures all changes since last full backup for rapid point-in-time restore |
| Transaction Log Backup | Every 5 minutes | 7 days | Continuous transaction logging enabling point-in-time recovery to any moment |
| Geo-Redundant Backup | Continuous replication | 30 days | Backups replicated to a geographically distant Azure region for disaster scenarios |
| Point-in-Time Restore | N/A | 30-day window | Ability to restore any database to any point within the last 30 days |
Geo-Redundancy
- Multi-region replication — Production data is continuously replicated to a secondary Azure region in a different geographic area
- Disaster recovery site — A standby environment in a geographically separate region is maintained in warm-standby mode, ready to assume production traffic
- Redundant power and connectivity — Azure data centers feature redundant power supplies, cooling systems, and network connections with diverse physical paths
Failover Mechanisms
Automated Failover
Azure SQL auto-failover groups detect database failures and automatically redirect connections to the secondary replica. Application services detect and re-route within seconds.
Blue/Green Deployment
Production deployments use Azure deployment slots (Blue/Green pattern) enabling instant rollback if any issue is detected during release. Zero-downtime deployments are standard.
Health Checks with Rollback
Automated health checks verify application functionality after each deployment. If checks fail, the previous version is automatically restored within seconds.
Circuit Breakers & Retry
Polly resilience library implements circuit breaker patterns and retry policies for all external service calls, preventing cascading failures across system components.
Recovery Objectives
| Metric | Target | Description |
|---|---|---|
| Recovery Time Objective (RTO) | 15 minutes | Maximum time from failure detection to service restoration using automated failover |
| Maximum Downtime | 4 hours | Absolute maximum downtime for worst-case disaster scenarios requiring full regional failover |
| Recovery Point Objective (RPO) | 5 minutes | Maximum acceptable data loss measured by the most recent recoverable transaction |
| Uptime SLA | 99.9% | Guaranteed minimum availability (equates to less than 8.77 hours unplanned downtime per year) |
| DR Exercise Frequency | Annual | Comprehensive disaster recovery exercises conducted annually with documented results |
Business Continuity Plan
ASDCom maintains a formal Business Continuity Plan (BCP) that encompasses the following elements:
- Business Impact Analysis (BIA) — Identifies critical business functions, dependencies, and acceptable disruption thresholds for each VCPMS component
- Risk Assessment — Comprehensive evaluation of threats, vulnerabilities, and their potential impact on service delivery
- MAO / RTO / RPO Definitions — Maximum Acceptable Outage, Recovery Time Objective, and Recovery Point Objective established for each service tier
- Annual Testing Program — The BCP is tested annually through multiple exercise types, with findings documented and remediated
Annual BC/DR Testing
| Exercise Type | Description | Frequency |
|---|---|---|
| Tabletop Exercise | Walk-through of disaster scenarios with key stakeholders to validate decision-making procedures | Annual |
| Simulated Failover | Controlled simulation of component failures to verify automated failover mechanisms operate correctly | Semi-annual |
| Partial DR Test | Activation of disaster recovery environment for specific components (database, application tier) to verify recoverability | Annual |
| Complete DR Test | Full failover to disaster recovery region with production workload validation, measuring actual RTO/RPO | Annual |
Disaster Type Assessment
| Disaster Type | Probability | Impact | Mitigation |
|---|---|---|---|
| Data Center Power Failure | Low | High | Redundant power, UPS, generator backup, multi-AZ deployment |
| Regional Network Outage | Low | High | Multi-region deployment, Azure Front Door traffic management, DNS failover |
| Ransomware / Cyberattack | Medium | Critical | Immutable backups, network segmentation, EDR, incident response plan |
| Database Corruption | Very Low | High | Point-in-time restore, integrity checks, geo-redundant replicas |
| Natural Disaster (earthquake, flood) | Very Low | Critical | Geo-separated disaster recovery region, automated failover |
| Application Deployment Failure | Medium | Medium | Blue/Green deployment, health checks, instant rollback, staging validation |
| Third-Party Service Outage | Medium | Medium | Circuit breakers, graceful degradation, retry policies, fallback mechanisms |
| Key Personnel Unavailability | Medium | Low | Cross-trained team, documented procedures, escalation matrix |
Escalation Matrix
Level 1: Operations Team (0-15 minutes)
Automated monitoring detects issue. On-call operations engineer acknowledges alert and begins diagnosis. Automated failover mechanisms activate for known failure patterns.
Level 2: Engineering Lead (15-30 minutes)
If Level 1 cannot resolve, engineering lead is engaged. Additional technical resources mobilized. Customer notification initiated for any user-impacting issues.
Level 3: CTO / CISO (30-60 minutes)
For major incidents or security breaches, executive leadership is engaged. Formal incident response plan activated. State customer security liaisons notified.
Level 4: Executive / External (1+ hours)
For critical incidents, CEO and legal counsel engaged. External communications, regulatory notifications, and law enforcement notification (if applicable) coordinated.
11. Vulnerability Management
VCPMS maintains a proactive vulnerability management program that identifies, assesses, and remediates security weaknesses before they can be exploited. The program combines automated scanning, manual penetration testing, and continuous monitoring to maintain the highest security posture.
Vulnerability Scanning
| Scan Type | Tool | Frequency | Scope |
|---|---|---|---|
| Static Application Security Testing (SAST) | Fortify / SonarQube | Every CI build | All application source code analyzed for vulnerabilities before merge |
| Dynamic Application Security Testing (DAST) | OWASP ZAP / Automated Suite | Nightly | Running application scanned for runtime vulnerabilities (XSS, SQLi, CSRF) |
| Dependency Scanning | OWASP Dependency-Check / Snyk | Every CI build | Third-party NuGet and npm packages checked against CVE databases |
| Infrastructure Scanning | Azure Security Center | Continuous | Cloud infrastructure configuration assessed against security baselines |
| Container Scanning | Azure Container Registry | On push | Container images scanned for OS and library vulnerabilities before deployment |
Penetration Testing
- Regular testing schedule — Penetration tests are conducted on a regular basis by both internal security staff and third-party testing firms
- Simulated attack scenarios — Tests simulate real-world attack vectors including social engineering, network penetration, application-level attacks, and insider threat scenarios
- CISO-scheduled annual tests — The Chief Information Security Officer schedules comprehensive annual penetration tests with findings reported to executive management
- Third-party testing — Independent security firms conduct blind and informed penetration tests to provide unbiased assessment of security posture
- Privacy impact assessments — Conducted whenever new features or integrations could affect the collection, storage, or processing of PII or PHI
Patch Management
| Category | Frequency | Details |
|---|---|---|
| Security Patches | Monthly (or emergency) | OS and framework security patches applied within the monthly maintenance window. Critical/zero-day patches applied within 24-48 hours |
| Feature Releases | Quarterly | New features and enhancements released quarterly with full regression testing |
| Standard Maintenance Window | 2nd Saturday, 12:00 AM - 6:00 AM | Scheduled maintenance window for patches and updates with minimal user impact |
| Post-Deployment Validation | Every deployment | Automated smoke tests verify core functionality after every patch or release |
| Rollback Capability | Always available | Instant rollback to previous version via Blue/Green deployment slot swap (less than 30 seconds) |
12. Secure Software Development Lifecycle (SDLC)
VCPMS is developed using a rigorous Secure Software Development Lifecycle (SSDLC) that integrates security at every phase — from requirements gathering through deployment and ongoing maintenance. Security is not a gate at the end of development; it is woven into every step of the process.
Secure Coding Practices
- OWASP Standards — All development follows OWASP Secure Coding Practices and the OWASP Top 10 mitigation guidelines
- Input Validation — All user inputs are validated on both client and server sides using whitelisting, type checking, length constraints, and format verification
- Parameterized Queries — All database interactions use parameterized queries or ORM-generated queries (Entity Framework Core), completely eliminating SQL injection risk
- SQL Injection Prevention — Automated SAST scans and code review hooks detect and block any raw SQL concatenation before code can be merged
- XSS / CSRF Protection — Angular's built-in XSS sanitization combined with ASP.NET Core's anti-forgery tokens protect against cross-site scripting and request forgery attacks
- Code Obfuscation — Production JavaScript bundles are minified and obfuscated to deter reverse engineering
- Runtime Defenses — Content Security Policy (CSP) headers, X-Frame-Options, X-Content-Type-Options, and Strict-Transport-Security headers are enforced on all responses
Code Review and Quality Gates
Peer Review
Every code change undergoes mandatory peer review. Pull requests require approval from at least 2 reviewers, including at least one senior developer with security expertise.
90% Code Coverage
The codebase maintains a minimum 90% code coverage target through unit tests, integration tests, and end-to-end tests. Coverage metrics are tracked and reported on every build.
Automated Regression
A comprehensive suite of automated regression tests runs on every pull request, catching regressions before they reach production. Tests cover unit, integration, and E2E scenarios.
Misuse Test Cases
In addition to functional tests, the test suite includes misuse test cases that deliberately attempt unauthorized access, injection attacks, and privilege escalation to verify defenses.
Development Security Infrastructure
- Git with GitFlow — All source code is managed in Git repositories using the GitFlow branching model, with protected branches and signed commits
- Quality gates — Automated quality gates in the CI pipeline block merges that fail SAST scans, unit tests, code coverage thresholds, or code review requirements
- Third-party component scanning — All NuGet packages (C#) and npm packages (TypeScript) are scanned against known vulnerability databases on every build
- Developer security certifications — ASDCom development team members hold industry-recognized security certifications including CISSP, CISA, and CompTIA Security+
- Source code escrow — Source code is maintained in escrow arrangements for state customers, ensuring continuity of operations even in unforeseen circumstances
Secure Deployment Pipeline
Build & Scan
Azure DevOps CI pipeline builds the application, runs SAST/DAST scans (Fortify, SonarQube), executes unit and integration tests, and checks third-party dependencies for vulnerabilities.
Manual Approval Gate
Deployment to staging and production requires explicit manual approval from authorized release managers. No automated promotion to production without human review.
Blue/Green Deployment (Slot Swap)
New version deployed to staging slot alongside running production. After validation, traffic is swapped in seconds. Previous version remains immediately available for rollback.
Health Checks & Validation
Automated health checks verify application functionality, database connectivity, and service availability. Smoke tests exercise critical user workflows automatically.
Instant Rollback
If any health check fails or an issue is reported, the deployment can be rolled back in under 30 seconds by swapping back to the previous slot. No data is lost.
Environment Configuration Separation
Each environment (development, staging, production) maintains completely separate configuration, secrets, and connection strings. No shared credentials or configuration between environments.
13. Privacy Controls
VCPMS is designed with privacy as a foundational principle, recognizing that victim compensation programs handle the most sensitive personal information about some of the most vulnerable members of society. The platform's privacy controls go beyond regulatory minimums to proactively protect victims of domestic violence, sexual assault, trafficking, and other crimes.
PII Protection
| Control | Implementation |
|---|---|
| Comprehensive PII Definition | PII encompasses names, SSNs, dates of birth, addresses, phone numbers, email addresses, medical records, financial data, biometric data, and any data that alone or combined could identify an individual |
| Collection Limits | The system collects only the minimum PII necessary to process victim compensation claims. Forms are designed to request only required fields, with optional fields clearly marked |
| Purpose Notification | Users are informed of the purpose for which their PII is collected through clear privacy notices displayed at the point of collection, with links to the full privacy policy |
| Secure Storage | All PII is stored in encrypted databases with field-level access controls. Sensitive fields (SSN, DOB) are additionally masked in the application layer |
| Retention Schedules | PII is retained only for the period required by state and federal regulations. Automated retention schedule enforcement ensures data is purged or archived on schedule |
| Data Masking | Dynamic data masking on screens, reports, and exports ensures users see only the PII they are authorized to access based on their role and permissions |
Privacy Principles
- Collect only as allowed by law — PII is collected only when authorized by applicable federal and state laws, and only for the specific purposes defined in those authorities
- Limit collection — The system is designed to collect the minimum amount of PII necessary to accomplish the stated purpose. Unnecessary data collection is prohibited
- No PII from browsing — VCPMS does not collect personally identifiable information from website browsing activities. No tracking cookies or behavioral analytics are used to identify visitors
- Inform of purpose — Individuals are notified of the purpose for data collection at the time of collection, including how the information will be used, shared, and protected
- Security safeguards — Appropriate administrative, technical, and physical safeguards are implemented to protect PII against loss, theft, unauthorized access, and disclosure
- SSL/TLS transmission — All data transmission uses SSL/TLS encryption. No PII is ever transmitted in cleartext over any network
- Staff training — All personnel who handle PII complete annual privacy training covering legal requirements, company policies, and incident reporting procedures
Communication Privacy: Virtual Secure Mail
VCPMS includes a Virtual Secure Mail (VSM) system that provides encrypted messaging between all parties in the compensation process — victims, claims staff, service providers, advocates, and law enforcement. VSM eliminates the need for paper mail and unencrypted email, providing critical safety protections.
- Encrypted messaging — All messages are encrypted in transit and at rest, with access limited to authenticated sender and recipient(s)
- Eliminates paper mail — Reduces the risk of sensitive documents being intercepted or discovered at a victim's physical address
- No unencrypted email — PII and case-related communications never travel through standard email, preventing interception and unauthorized access
- Protects DV/SA/trafficking survivors — Particularly critical for victims of domestic violence, sexual assault, and human trafficking, where physical mail or standard email could be monitored by perpetrators and endanger victim safety
Mobile Device Security
- PII not stored on devices — VCPMS is a web-based application that does not store PII on mobile devices or local storage unless specifically required for offline functionality
- Privacy impact assessments — Conducted before any mobile-accessible feature is released to evaluate PII exposure risk on mobile platforms
- Encryption required — Any device accessing VCPMS must have full-disk encryption enabled as verified by device compliance policies
- BYOD prohibitions — Personal devices used to access VCPMS must meet minimum security requirements enforced through Azure AD conditional access policies
14. Confidentiality
Strict confidentiality requirements are enforced for all personnel who have access to VCPMS systems or the data contained within them. These requirements extend beyond employment, creating enduring obligations that protect victim information indefinitely.
Confidentiality Statement Requirements
- Universal requirement — All employees, volunteers, contractors, and subcontractors must sign a comprehensive Confidentiality Statement before receiving any access to VCPMS systems or data
- Job-duty access only — Access to confidential information is permitted only when directly required for the performance of assigned job duties. No exceptions
- No curiosity access — Accessing records out of personal curiosity, interest, or any purpose unrelated to job responsibilities is strictly prohibited and subject to disciplinary action
- Secure storage — Any physical copies of confidential information must be stored in locked containers within secured areas accessible only to authorized personnel
- Disclosure restrictions — Confidential information may not be disclosed to any person, organization, or entity except as authorized by law or with explicit approval from the program administrator
- Law enforcement report protection — Law enforcement reports and criminal justice information receive the highest level of confidentiality protection in accordance with CJIS requirements
Ongoing Obligations
- Continue post-employment — The duty to protect confidential information survives termination, resignation, or contract completion with no expiration date
- Certification in personnel file — Signed Confidentiality Statements are maintained in personnel files as permanent records
- Violations subject to discipline, prosecution, and lawsuit — Breach of confidentiality may result in immediate termination, criminal prosecution under applicable federal and state laws, and civil liability for damages
15. Staff Vetting
ASDCom implements comprehensive personnel security measures to ensure that all individuals with access to VCPMS systems and victim data are trustworthy, qualified, and appropriately screened. These measures exceed industry standards and align with CJIS personnel security requirements.
Background Checks
| Check Type | Scope | Applies To |
|---|---|---|
| Criminal Record Check | Federal and state criminal history databases | All employees, contractors, and volunteers |
| Fingerprint-Based Check | State and FBI fingerprint databases | Personnel with access to CJIS data |
| Employment Verification | Previous employer confirmation of dates, titles, and performance | All employees |
| Reference Checks | Professional and character references | All employees and key contractors |
| Education Verification | Degree and certification verification | Technical and security personnel |
Personnel Security
- Trusted status required — Privileged access to production systems (database administration, system configuration, key management) is granted only to personnel who have achieved trusted status through comprehensive vetting
- Oaths of confidentiality — All personnel sign oaths of confidentiality before receiving system access, with annual renewal and acknowledgment
- Regular screening — Background checks are not one-time events. Personnel in sensitive positions undergo periodic re-screening to ensure continued eligibility
- Security clearance tracking — For CJIS-related deployments, security clearance status is tracked and maintained, with automatic access revocation for lapsed clearances
Termination Procedures
- Debriefing — Departing personnel receive a formal security debriefing reminding them of ongoing confidentiality obligations
- Access revocation — All system access, VPN credentials, email accounts, and physical access tokens are revoked immediately upon separation (within 1 hour of notification)
- Security item retrieval — All company-issued devices, access badges, authentication tokens, and documentation are retrieved and inventoried before departure
- Post-departure audit — Recent access logs for the departing individual are reviewed for any unusual activity preceding their departure
16. Network Security
VCPMS network architecture is designed to minimize attack surfaces while maintaining the performance and reliability required for state government operations. Multiple layers of network security controls protect data at every point in the communication path.
Network Architecture Controls
- Documented network details — Complete network architecture documentation is maintained, including topology diagrams, IP addressing schemes, firewall rules, and data flow diagrams
- Redundancy — Network infrastructure includes redundant paths, load balancers, and failover mechanisms to eliminate single points of failure
- Minimized entry points — Public-facing endpoints are limited to the minimum necessary (HTTPS load balancers only). All other infrastructure is accessible only through private networks
- Secure protocols only — Only approved secure protocols are permitted (TLS 1.2+, SSH, SFTP). Legacy protocols (FTP, Telnet, SSL, TLS 1.0/1.1) are explicitly blocked
- Firewalls — Azure Network Security Groups (NSGs) and Azure Firewall provide multi-layer firewall protection with deny-by-default policies
- Vendor defaults changed — All default vendor credentials, ports, and configurations are changed before deployment. Default accounts are deactivated
- Guest accounts deactivated — No guest or anonymous accounts exist in any VCPMS infrastructure. All access requires authenticated identity
Network Security Measures
Per-Customer Firewalls
Each state customer's environment includes dedicated firewall rules isolating their traffic from all other tenants. IP-based access control lists (ACLs) restrict access to authorized networks.
IDS / IPS
Intrusion Detection and Prevention Systems monitor all network traffic for malicious patterns, automatically blocking known attack signatures and alerting on suspicious activity.
DDoS Protection
Azure DDoS Protection Standard provides always-on monitoring and automatic mitigation of volumetric, protocol, and application-layer DDoS attacks targeting VCPMS infrastructure.
Public / Private Subnets
Infrastructure is segmented into public-facing subnets (load balancers only) and private subnets (application and database tiers), with strict network security group rules governing inter-subnet traffic.
VPN / MFA for Administration
All administrative access to infrastructure requires VPN connectivity with multi-factor authentication. No administrative ports are exposed to the public internet.
No External Cloud Access
No external third party has direct access to the VCPMS cloud infrastructure. All integrations operate through secure APIs with authenticated, authorized, and rate-limited access.
17. Physical Security
All VCPMS infrastructure is hosted in Microsoft Azure data centers, which implement world-class physical security measures. ASDCom does not operate its own data centers; instead, it leverages Azure's industry-leading physical security controls.
Data Center Physical Security
| Control | Description |
|---|---|
| 24/7 Security Guards | Azure data centers are monitored around the clock by professional security personnel with access to surveillance systems |
| Perimeter Security | Multiple security perimeters with barriers, surveillance cameras, motion sensors, and controlled vehicle access points |
| Locked Cages & Cabinets | Server equipment is housed in individually locked cages and cabinets with electronic access controls and audit logging |
| No Customer Entry | Customers do not have physical access to Azure data centers. All management is performed remotely through Azure's management plane |
| Redundant Power | Uninterruptible power supplies (UPS), diesel generators, and multiple utility feeds ensure continuous operation during power disruptions |
| Environmental Controls | Advanced fire detection/suppression, temperature/humidity monitoring, and flood protection systems protect equipment |
| Biometric Access | Multi-factor physical access controls including biometric scanners, smart cards, and PINs for all personnel entering secure areas |
Physical Access Controls
- Key/card lock systems — All physical access points use electronic card readers with audit trails recording entry and exit times for all personnel
- Authorization required — Physical access to data center facilities requires prior authorization through a formal request and approval process
- Visitor escort policy — All visitors to data center facilities must be pre-approved, identification-verified, and escorted at all times by authorized personnel
- Media disposal — Failed or decommissioned storage media undergo NIST 800-88 compliant sanitization (degaussing, destruction, or cryptographic erasure) before leaving the facility
18. Work-From-Home Security
ASDCom recognizes that modern workforce arrangements include remote and hybrid work. Comprehensive work-from-home security policies ensure that remote access to VCPMS development and operations environments maintains the same security standards as on-premises access.
Remote Work Security Requirements
Secure Wi-Fi
Remote workers must use WPA3 or WPA2-Enterprise encrypted wireless networks. Public Wi-Fi and open networks are prohibited for VCPMS access without VPN protection.
Anti-Virus & Security Software
All devices used for VCPMS work must have current anti-virus/anti-malware software installed and actively monitoring. Endpoint Detection and Response (EDR) is required.
Security Software Updates
Operating systems, browsers, and security software must be kept current with automatic updates enabled. Devices that fall behind on patches are blocked from accessing VCPMS.
Backup Strategy
Work-related data must not be stored solely on local devices. All work is performed in cloud-hosted environments, with local device backup policies enforced for company-issued equipment.
Screen Locking
Automatic screen lock is required after 5 minutes of inactivity on all devices used for VCPMS work. Manual lock is required when leaving the workstation unattended.
Full-Disk Encryption
All devices must have full-disk encryption enabled (BitLocker for Windows, FileVault for macOS). Encryption status is verified by Azure AD device compliance policies.
Incident Procedures
Remote workers are provided with clear incident reporting procedures to follow in the event of a security incident, device loss, or suspected compromise:
- Immediately report any suspected security incident to the ASDCom security team via the designated security hotline or secure messaging channel
- For lost or stolen devices, report immediately so that remote wipe can be initiated and access credentials can be revoked
- Preserve any evidence of the incident (screenshots, error messages, suspicious communications) for investigation
- Do not attempt to independently investigate or remediate security incidents — follow the established incident response chain
19. Monitoring & Incident Response
VCPMS implements comprehensive monitoring and incident response capabilities that provide 24/7 visibility into system health, security posture, and operational performance. The monitoring infrastructure is designed to detect anomalies early, alert responders quickly, and provide the diagnostic data needed for rapid resolution.
System Monitoring
| Monitoring Capability | Technology | Details |
|---|---|---|
| Application Performance | Azure Monitor / Application Insights | Real-time telemetry covering request rates, response times, failure rates, dependency calls, and user sessions |
| Custom Alerts | Azure Monitor Alerts | Configurable alert thresholds (e.g., 5% error rate trigger) with email, SMS, and webhook notification channels |
| Centralized Logging | Azure Log Analytics (JSON-structured) | All application and infrastructure logs aggregated in a central, searchable repository with 90-day retention |
| Query Analytics | Kusto Query Language (KQL) | Powerful query capabilities for investigating incidents, identifying trends, and generating security reports |
| Health Monitoring | Azure Health Checks / Uptime Robot | 24/7 endpoint monitoring with sub-minute check intervals and instant notification of outages |
| Security Event Monitoring | Azure Security Center / Sentinel | Continuous security posture assessment, threat detection, and security recommendations |
Incident Response
- Comprehensive logging — All security events, access attempts, configuration changes, and data operations are logged with sufficient detail for forensic investigation
- Breach disclosure — In the event of a confirmed data breach, ASDCom will notify affected state customers within 24 hours in accordance with contractual obligations and applicable breach notification laws
- Escalation matrix — A formal escalation matrix (see Section 10) defines roles, responsibilities, and communication paths for incidents of varying severity
- Immediate notification — Critical security events (unauthorized access attempts, data exfiltration indicators, service compromises) trigger immediate automated notifications to the security team
Resilience Patterns
Polly Retry & Circuit Breakers
The Polly resilience library implements retry policies with exponential backoff and circuit breaker patterns for all external service calls, preventing cascading failures during partial outages.
Graceful Degradation
When non-critical services are unavailable, VCPMS continues operating with reduced functionality rather than failing entirely. Core claims processing and data access remain available.
User-Friendly Error Messages
Technical errors are never exposed to end users. Instead, friendly, actionable error messages are displayed while detailed technical information is logged for engineering investigation.
Screenshot: VCPMS operations dashboard showing real-time system health metrics, active alerts, and performance indicators — Available upon request
Why Choose VCPMS Security
Enterprise-Grade Protection
Multi-layered defense-in-depth security architecture designed to protect the most sensitive categories of data in government systems — PII, PHI, criminal justice records, and financial transactions — with controls that meet or exceed federal standards.
Regulatory Compliance
Comprehensive alignment with HIPAA, CJIS Security Policy, FedRAMP, FIPS 140-2, NIST 800-53, VOCA/OVC requirements, and WCAG 2.1 AA accessibility standards, with documented control mappings available for state security review.
Azure Cloud Security
Backed by Microsoft's industry-leading cloud security with US-only data centers, Azure Government Cloud option for CJIS, FedRAMP-certified infrastructure, and the most comprehensive set of compliance certifications in the cloud industry.
Zero-Trust Architecture
Every access request is verified regardless of origin. Mandatory MFA for all users, role-based access control at four levels (system, page, field, document), and encrypted communications across every network segment.
Business Continuity
99.9% uptime SLA with 15-minute RTO, geo-redundant backups, automated failover, Blue/Green deployments, and comprehensive disaster recovery plans tested annually through tabletop exercises and full failover tests.
Transparent Auditing
Tamper-proof, read-only audit trails recording every significant action in the system — who, what, when, and where — providing complete accountability for compliance reviews, appeals, and fraud investigations.